Lesson 2: Security CIA, Protection & Least Privilege Concepts
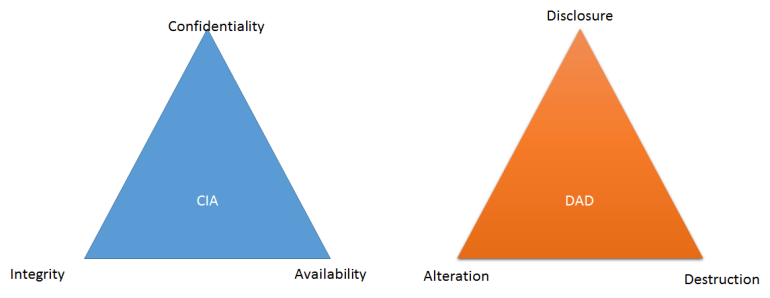
The CIA Triad
All issues and solutions pertaining to security fall under 3 categories:
- Confidentiality – Protection against unauthorized access
- Integrity – Protection against unauthorized modification
- Availability – Protection against denial of service
The exact opposite of the CIA is the DAD – Disclosure, Alteration and Destruction.
See the following events and solutions:
- Locking the door when you leave the house – This is a confidentiality solution because only the person who has the key to unlock the door can enter the house.
- A students overwrites the teacher’s Powerpoint presentation – This is an integrity issue because the content of the presentation is already changed.
- The system administrator backs up the file server every Friday – This is an availability solution because the backup ensures access to the files when the main file server becomes unavailable.
A security issue can be a result of an accidental or intentional event. In example 2, the student may have accidentally overwritten the teacher’s file because of his negligence. He may also have overwritten the file intentionally out of revenge. But regardless of his intention, it is classified as a security issue.
The Formula for Protection
Some decades ago, the formula for protection is:
This means that in order to protect something, you need to prevent something bad from happening. For example, in order to prevent a home intruder from entering your home, you install a gate around your house. You are preventing the intruder from getting in the house because of the gate.
Similarly in the technical world, you can install a firewall in your network. A firewall is a hardware or software that enforces a security policy. For example, you have a web server in your company and you would like the public only to access the web server, the firewall can filter the traffic going to your network. Only packets/traffic that are destined to TCP port 80 (http) will be allowed to enter the network. That’s because port 80 is specifically opened for web connections. All other traffic will be denied.
Now, what is the problem or limitation with this formula?
In the first example (gate example), what will happen if the intruder climbs using a rope and he is able to pass the gate? Hypothetically, if the intruder is able to enter your house in the middle of the night, will you be able to stop him?
The formula for protection lacks other components.
Let’s say you bought a motion sensor alarm and a gun. You realize that if the intruder is able to enter your house after passing the gate using a rope, the motion sensor alarm will detect his movements and will alert you. Now if you see him and he’s planning to attack you with some weapon, you can defend yourself by shooting him using your gun.
Well, that’s just a hypothetical situation. But the point is, you need to anticipate that your preventive tool may be bypassed. That’s why you need to set up other security controls.
Therefore, the modified and correct formula for protection is:

Protection = Gate + (Motion Sensor Alarm + Shoot using your gun)
This formula can be applied to all domains of information security.
Going back to the firewall example, can you determine the limitation of implementing only a firewall in your network? If the firewall is the preventive tool, what is the detective tool and the response mechanism?
Least Privilege
I think the concept of least privilege is the essence of information security. In least privilege, you only get the privilege and access that you need, nothing more and nothing less.
In a company, there is an Accountant, HR assistant and Sales Agent. When we apply least privilege to these 3 employees, we will give each employees the following access to applications:
Accountant – MS Excel, Calculator, E-mail, Printer
HR Assistant – Telephone, Job Street, LinkedIn, MS Word, E-mail, Printer
Sales Agent – Telephone, Facebook, MS Word, E-mail, Printer
In least privilege, we list the things that each employee needs and we give the needed access to them. However, those applications that are not in the list won’t be given to the users.
Types of Least Privilege
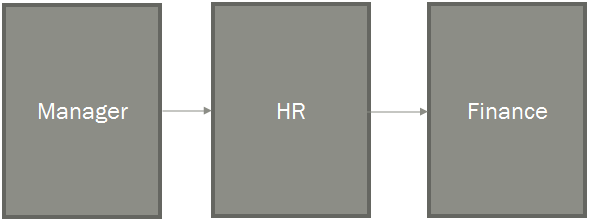
Separation of Duties (SOD)
SOD states that a task (especially critical jobs) must be delegated to more than 1 person. Let’s use the payroll system as an example.
HR Department – Computes your daily time record (DTR)
Accounting Department – Computes your salary based of the DTR submitted by HR department
Management Group – Approves the salary computed and submitted by the Accounting department
What happens if only one person, let’s say Paula, computes for the DTR and salary and approves the computation also?
For instance, if an employee, Gilbert, does not go to work, then it will reflect in his DTR. However, if Paula decides to give Gilbert a salary, then she can freely do so without anybody questioning it. There’s nobody who checks if the task is done correctly or not.
The SOD for the payroll scenario is very important to ensure checks and balances of activities related to work.
Implicit Deny
Implicit Deny is another type of least privilege that is usually seen and applied in a firewall Access Control List (ACL). Assuming we have an entry in an access control list:

This ACL entry allows web traffic (tcp 80) going in and out of the network. If that’s the only rule that we have in the ACL, can we access the file server in the network (tcp 21)?
The answer, of course, is no. But one can ask, will it deny tcp 21 even if there is not rule stating that it should be denied?
The implicit deny states that if there is no rule that states allow, then deny access. So even without a specific rule, it is understood that there is a “deny all” rule after the last entry in the ACL.
Job Rotation
Job Rotation is a not so known type of least privilege. This concept requires that other persons are familiar with the job that you have especially if it is a critical role. Although it is costly because you need to train other employees, this is very helpful in determining what is happening to the tasks assigned to a particular person.
If you are put in an employee’s shoes due to job rotation, you and the management may find a lot of things. For example, why does this employee take 10 hours (with overtime) to do his job when I can finish it in 4 hours when I assumed his role in job rotation? There may be something to investigate in this issue.
—– NOTHING FOLLOWS —–